Secure Your Digital Assets: The Power of Managed Information Protection
In an age where data violations and cyber dangers are progressively prevalent, safeguarding electronic properties has emerged as a paramount worry for organizations. Taken care of data security provides a strategic opportunity for companies to integrate advanced protection measures, making certain not just the protecting of delicate details but also adherence to regulative requirements. By contracting out data security, business can focus on their main objectives while professionals browse the complexities of the electronic landscape. Yet, the efficiency of these options pivots on several elements that necessitate cautious consideration. What are the critical components to keep in mind when exploring handled data security?
Comprehending Managed Information Defense
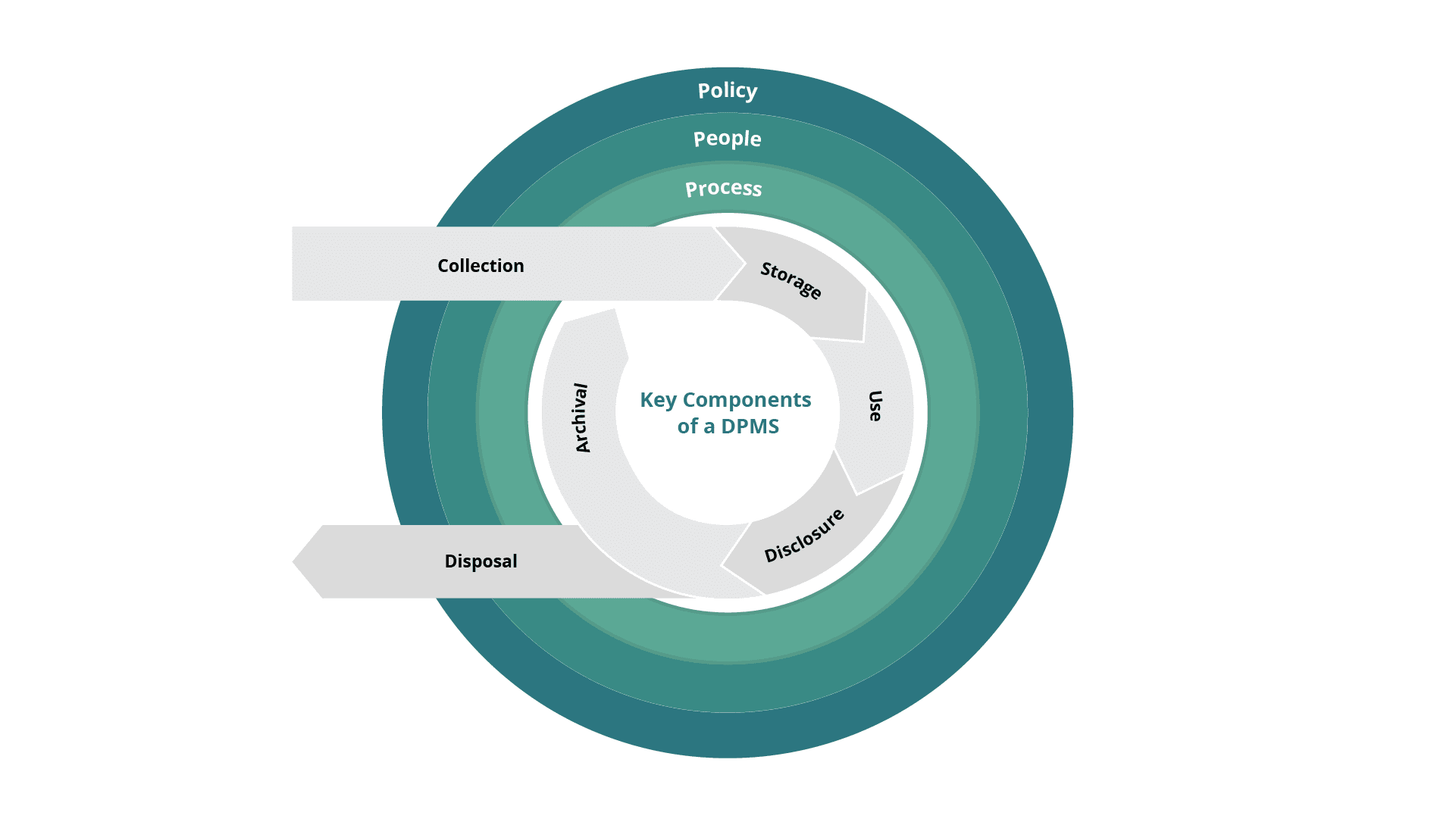
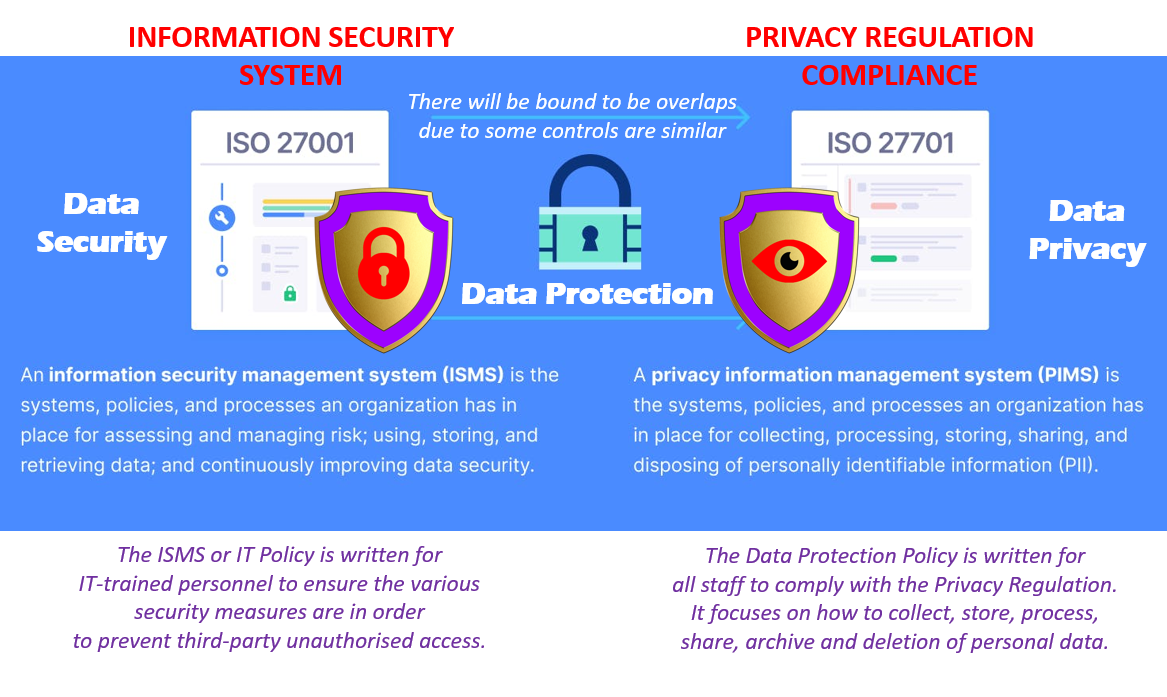
Key components of managed data protection include information back-up and healing solutions, encryption, accessibility controls, and continuous monitoring. These components operate in performance to produce a durable security framework - Managed Data Protection. Normal back-ups are important, as they supply recuperation options in case of data loss as a result of equipment failing, cyberattacks, or all-natural calamities
Security is an additional vital part, changing delicate information into unreadable styles that can only be accessed by licensed customers, thereby alleviating the threat of unauthorized disclosures. Accessibility manages better improve safety and security by guaranteeing that only individuals with the appropriate approvals can communicate with sensitive info.
Constant tracking permits organizations to react and detect to potential dangers in real-time, therefore bolstering their overall data stability. By implementing a taken care of data security approach, organizations can attain better durability against data-related dangers, guarding their operational continuity and keeping trust fund with stakeholders.
Advantages of Outsourcing Data Safety And Security
Contracting out information safety and security offers various advantages that can significantly boost an organization's general safety position. By partnering with specialized took care of safety provider (MSSPs), companies can access a wide range of knowledge and sources that might not be available in-house. These service providers employ competent experts that stay abreast of the most recent threats and protection steps, making certain that companies benefit from current finest modern technologies and methods.
Among the main benefits of outsourcing information safety is cost performance. Organizations can minimize the economic problem related to hiring, training, and maintaining in-house safety workers. In addition, outsourcing permits firms to scale their protection measures according to their progressing needs without incurring the dealt with prices of keeping a permanent safety and security team.
Additionally, contracting out allows organizations to concentrate on their core business features while leaving complicated safety jobs to professionals - Managed Data Protection. This critical delegation of obligations not only improves operational performance yet additionally fosters a proactive safety culture. Ultimately, leveraging the capabilities of an MSSP can result in improved risk discovery, lowered feedback times, and a more durable safety and security structure, positioning organizations to browse the dynamic landscape of cyber hazards successfully
Key Attributes of Managed Services
Organizations leveraging managed security services generally take advantage of a suite of vital functions that improve their information protection strategies. Among the most considerable features is 24/7 surveillance, which makes certain consistent vigilance over information atmospheres, enabling quick detection and action to threats. This day-and-night defense is complemented by advanced risk knowledge, permitting organizations to stay in advance of arising dangers and susceptabilities.
An additional essential attribute is automated information backup and healing remedies. These systems not just secure information stability yet additionally improve the healing procedure in case of data loss, guaranteeing service continuity. In addition, handled solutions frequently include comprehensive conformity administration, helping organizations navigate complex laws and keep adherence to industry criteria.
Scalability is also an essential element of taken care of services, making it possible for organizations to adapt their information defense determines as their needs develop. Professional assistance from dedicated protection experts offers organizations with accessibility to specialized expertise and understandings, boosting their total protection posture.
Selecting the Right Company
Selecting the right carrier for taken care of information defense services is critical for guaranteeing robust safety and conformity. The initial step in this process involves examining the supplier's reputation and performance history. Search for established organizations with tried and tested experience in data security, particularly in your sector. Testimonials, situation researches, and customer endorsements can offer useful understandings into their dependability and performance.
Following, assess the range of solutions offered. A comprehensive took care of data defense service provider should consist of information back-up, recovery options, and recurring surveillance. Ensure that their solutions straighten with your certain organization requirements, consisting of scalability to accommodate future development.
Compliance with market regulations is an additional vital aspect. The carrier must comply with relevant standards such as GDPR, HIPAA, or CCPA, depending on your field. Inquire concerning their conformity accreditations and methods.
Furthermore, think about the modern technology and devices they make use of. Companies should utilize advanced safety measures, consisting of file encryption and danger discovery, to guard your information successfully.
Future Trends in Information Security
As the landscape of data defense continues to progress, numerous essential patterns are emerging that will certainly shape the future of handled data defense services. One noteworthy pattern is the raising adoption of expert system and artificial intelligence technologies. These tools improve data defense strategies by allowing real-time threat discovery and action, hence decreasing the time to mitigate possible breaches.
An additional significant pattern is the shift in the direction of zero-trust safety and security versions. Organizations are acknowledging that conventional perimeter defenses are inadequate, resulting in a much more durable structure that continually verifies customer identifications and device honesty, no matter their area.
Additionally, the increase of governing conformity requirements is pushing organizations see page to embrace even more detailed information defense steps. This consists of not just protecting information but additionally guaranteeing openness and accountability in information taking care of techniques.
Finally, the integration of cloud-based options is transforming information security techniques. Taken visit this web-site care of data defense services are significantly making use of cloud modern technologies to provide scalable, flexible, and cost-efficient solutions, enabling organizations to adapt to changing risks and demands properly.
These patterns underscore the value of proactive, ingenious techniques to information protection in a significantly complex electronic landscape.
Conclusion
In final thought, handled data protection arises as a vital technique for companies looking for to secure digital properties in an increasingly complicated landscape. Inevitably, accepting taken care of data defense allows organizations to concentrate on core procedures while making certain comprehensive protection for their useful site digital possessions.
Key components of managed data security include data backup and recuperation options, file encryption, access controls, and continuous surveillance. These systems not only guard information stability yet additionally streamline the healing procedure in the occasion of information loss, making certain service continuity. A comprehensive handled information defense supplier must include data back-up, healing solutions, and continuous surveillance.As the landscape of information defense proceeds to evolve, numerous key fads are emerging that will certainly shape the future of taken care of information security services. Inevitably, accepting taken care of information protection permits companies to concentrate on core operations while guaranteeing extensive safety and security for their digital possessions.